
Ten tips to prevent cyber attacks
by bernt & torsten
Cyber attacks are on the increase for both private individuals and sensitive businesses with today’s seriously deteriorating world situation. The current situation leads to foreign powers increasing their need to obtain sensitive information about a country’s interests. Or something else that can affect the national security or that of activities that are necessary for the country to be able to function.
And in order to access the information worthy of protection or influence countries, foreign power can be used in different ways:
– It’s everything from recruiting spies and conducting espionage, illegal intelligence gathering in a country, that you are interested in information in order to gain an advantage and understand what decisions may be made. That’s a lot. But there are also influence operations, cyber attacks, illegal collection of information through cyber attacks.
The ten tips for cybersecurity:
- Install security updates as soon as possible
Prioritize updating information systems that are exposed to the Internet, those that are business-critical and those where vulnerabilities are at risk of being exploited. Aim to install security updates as soon as they are published. - Manage permissions and use strong authentication features
Control all accounts in the IT environment, disable unused ones. Be strict with the permissions assigned. Use multi-factor authentication on all publicly exposed services, for access to high value information and for accounts with system administrative privileges. Where multi-factor authentication is not supported, use unique and long passwords. - Restrict and protect the use of system administrative privileges
Use separate accounts for system administrative privileges. Also limit the system administrative competencies to tasks, roles and parts of the IT environment. Do not assign system administrative privileges to regular users. - Disable unused services and protocols (harden systems)
Ensure that functions that are not needed for the desired functionality of the information systems are turned off, blocked or uninstalled. Configure the information systems to have a high level of security. - Make backups and test if the information can be read back
Create backups of information based on the needs of the business. Handle the backups securely and periodically test that it is possible to restore the information based on the backups taken. - Only allow approved equipment on the network
Only allowed equipment may be connected to the network. Unauthorized equipment needs to be detected and its access to services and information in the IT environment prevented. - Ensure that only approved software may be run (whitelisting)
Only permitted software may be run in the IT environment. Prevent unauthorized software from running. - Segment the networks and filter the traffic between the segments
Create different network segments and create controlled traffic flows between the segments with the help of filtering functions that protect against unwanted traffic flowing freely in the network. - Upgrading software and hardware
Replace and replace outdated hardware and software to counteract vulnerabilities that have been exposed over time and to achieve the intended function and adequate security. - Ensure an ability to detect security incidents
Acquire the ability to detect security incidents in the IT environment as early as possible. Monitor events in the IT environment with manual, technical and automatic measures. Create security logs that can be used for monitoring and that are protected against unauthorized access or alteration.

Tech Disillusionment
For four decades, I have worked in the tech industry. I started in the 1980s when computing...
A Poem: The Consultant's Message
On a Friday, cold and gray,
The message came, sharp as steel,
Not from those we...
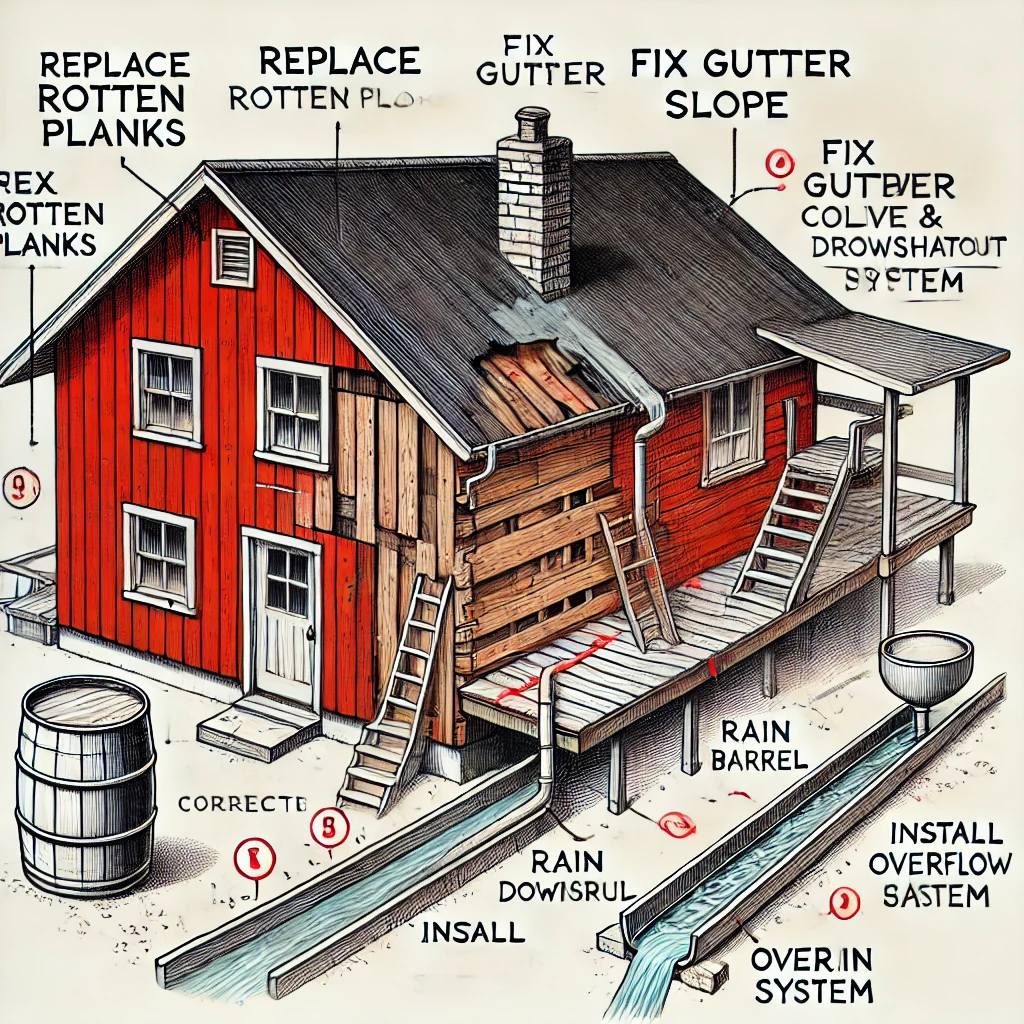
Using AI to Plan Wall Repair and Gutter Installation
In this article, I will share my experience using AI to plan the work required to fix a wall...