
Exploring Cybersecurity: Tools and Techniques for Ethical Hacking
by bernt & torsten
When it comes to cybersecurity, there are numerous roles and specializations available. It’s beneficial to immerse yourself in cyber content to determine your area of interest. This can include podcasts, books, YouTube videos, or online training courses.
Consider what aspects of cybersecurity intrigue you. If you come from a data science background and are passionate about data, cybersecurity data science might be a perfect fit. Loving what you do is crucial because it doesn’t feel like a chore when you enjoy your work. It fuels your curiosity and motivates you to go the extra mile. In cybersecurity, an insatiable appetite for knowledge sets candidates apart, even those who graduated from the same institute with similar grades. Now, let’s delve into some essential tools you need.
Virtual Machines (VMs) will become your closest allies. Not only are they environmentally friendly compared to building physical labs, but they also allow you to replicate scenarios (to a certain extent, depending on your machine’s power) and provide an opportunity to become comfortable with the command line.
VirtualBox is the most popular open-source virtualization tool for deploying VMs. A common practice is to set up a vulnerable machine, such as a mail server with a known vulnerability, and another VM running Kali Linux or Parrot OS. By configuring the network settings to enable communication between them, you can start exploring exploitation techniques.
Now, let’s discuss which operating systems you should try out.
Kali Linux is often recommended, especially for penetration testing. However, Kali is a comprehensive toolkit with numerous tools, making it overwhelming for first-time users. So, how can you become proficient with it?
Practice makes perfect!
Let’s say you’re a Database Administrator (DBA) with extensive experience working with databases, but now you want to transition to the infosec side. You’re familiar with databases but have never used Kali. The best way to learn is by creating a VM with MongoDB and installing a version known to have vulnerabilities. In the cybersecurity world, vulnerabilities are often categorized using Common Vulnerabilities and Exposures (CVEs). For example, searching for MongoDB vulnerabilities will yield 36 CVEs, all of which have been patched.
However, suppose you download and install an unpatched version of MongoDB on a VM, such as one vulnerable to CVE-2015–7882, which allowed unauthorized access due to improper handling of LDAP authentication in versions 3.0.0 to 3.0.6. In that case, you can practice using tools like Metasploit or other database cracking tools. The principle behind this approach is to get hands-on experience with the toolkits available in Kali, switching between databases and tools while learning the basics of penetration testing. Many believe that the best defence comes from understanding the attack. Therefore, gaining knowledge about how systems can be compromised is essential in cybersecurity.
However, it’s important to note that cybersecurity encompasses more than just penetration testing.
One of my favourite VMs in this regard is Security Onion. It’s a comprehensive security suite that can enhance your home defence practices. It provides an excellent opportunity to use your data to learn. Let’s explore what Security Onion has to offer.
Security Onion is a free, open-source Linux distribution for intrusion detection, enterprise security monitoring, and log management. It incorporates various security tools such as Elasticsearch, Logstash, Kibana, Snort, Suricata, Bro, Wazuh, Sguil, Squert, CyberChef, NetworkMiner, etc.
In summary, cybersecurity offers a wide array of roles and specializations. You can expand your expertise in ethical hacking and cybersecurity by familiarizing yourself with relevant tools and techniques, such as virtual machines, Kali Linux and Security Onion.
Another essential tool worth mentioning is Metasploit. It is a robust framework that enables penetration testers to exploit vulnerabilities in systems and applications. Metasploit provides a vast collection of exploits, payloads, and auxiliary modules, allowing you to simulate real-world attack scenarios and assess the security posture of target systems.
Wireshark is another indispensable tool for ethical hackers. It is a network protocol analyzer that allows you to capture and analyze network traffic. By examining packets flowing through a network, you can identify potential security vulnerabilities, detect malicious activities, and gain a deeper understanding of network protocols.
Nmap (Network Mapper) is a versatile and widely used network scanning tool. It helps discover hosts and services on a network, map the network topology, and identify open ports and available services. Nmap provides valuable information for surveillance and vulnerability assessment, enabling you to assess the security of a network and its assets.
For web application security testing, Burp Suite is a popular choice. It is a comprehensive suite of tools designed to analyze the security of web applications. Burp Suite allows you to intercept and modify HTTP/S requests, crawl web applications for vulnerabilities, and automate security testing tasks. It is an essential tool for identifying common web application vulnerabilities, such as cross-site scripting (XSS) and SQL injection.
To strengthen your understanding of wireless network security, tools like Aircrack-ng come into play. Aircrack-ng is a suite of tools used for assessing the security of Wi-Fi networks. It includes capabilities for capturing and analyzing network packets, cracking WEP and WPA/WPA2-PSK encryption, and performing various wireless attacks. By familiarizing yourself with Aircrack-ng, you can assess the vulnerabilities present in wireless networks and implement adequate security measures.
These are just a few examples of the various tools available to ethical hackers and cybersecurity professionals. It’s essential to continuously expand your knowledge and stay updated with the latest techniques and tools as the cybersecurity landscape evolves rapidly.
Remember, ethical hacking involves using these tools and techniques for legitimate and authorized purposes, ensuring systems and data protection. Ethical hackers are crucial in identifying vulnerabilities, enhancing security measures, and safeguarding organizations from malicious attacks.
In conclusion, by immersing yourself in cybersecurity content, experimenting with virtual machines, and exploring tools like Kali Linux, Metasploit, Security Onion, and others, you can develop the skills and knowledge necessary to excel as an ethical hacker and contribute to the ever-growing field of cybersecurity.

Tech Disillusionment
For four decades, I have worked in the tech industry. I started in the 1980s when computing...
A Poem: The Consultant's Message
On a Friday, cold and gray,
The message came, sharp as steel,
Not from those we...
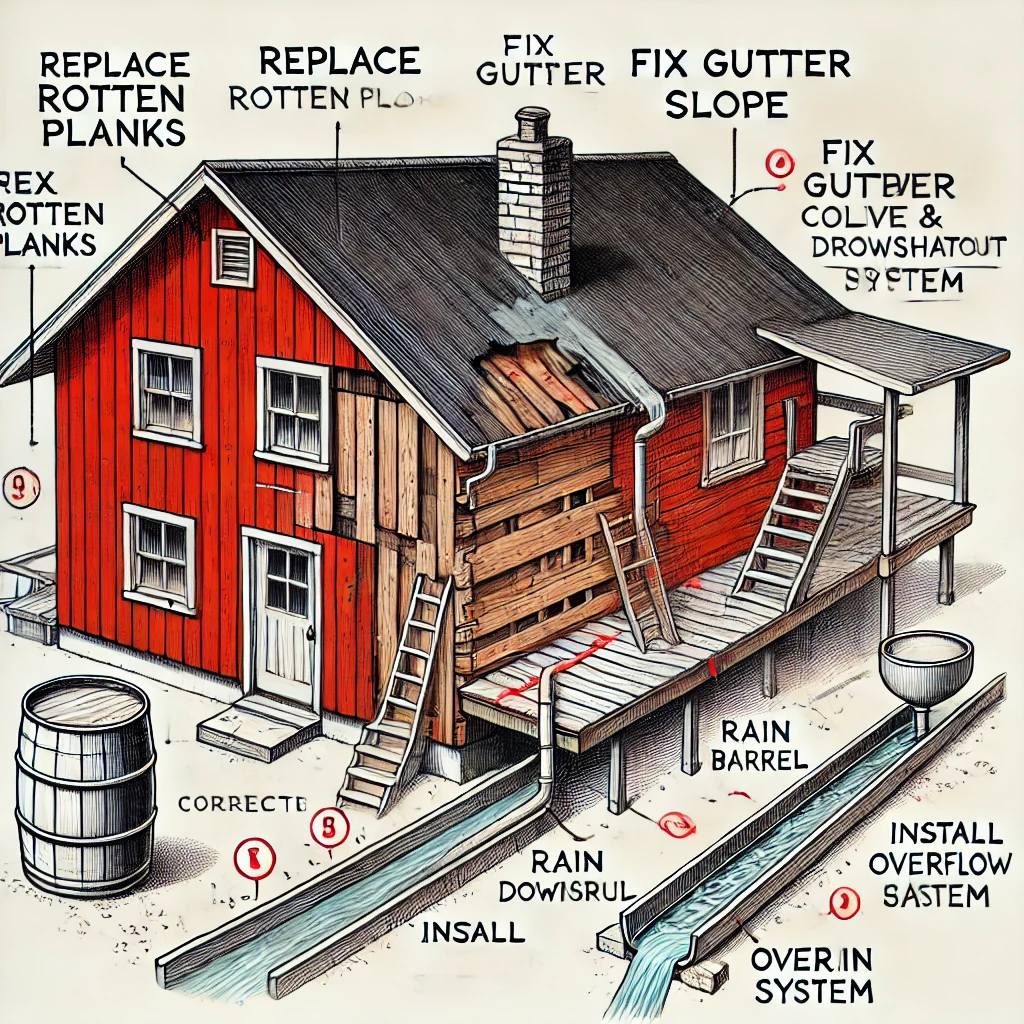
Using AI to Plan Wall Repair and Gutter Installation
In this article, I will share my experience using AI to plan the work required to fix a wall...