
Can you stay anonymous online
by bernt & torsten
From the early days of information technology, data was collected, it was primarily banks and credit card companies that collected data on the cardholders and later came supermarkets with the store cards. In the early day, most data was used to do statistical analysis.
With the advent of the internet for everyone, through numerous providers such as hughesnet internet, for example, the explosion of data collection took off, and many businesses built a business around collecting data and offered these services to other businesses. The Internet was built on anonymity, paving the way for a place where free speech would rule. With businesses tracking what we are doing online, privacy on the internet is hard to do if you don’t know what to do to keep your privacy.
Everyone is tracking you online, big companies like Amazon, Twitter, Google, Facebook and Microsoft collect a lot of data on you to serve up targeted ads. A lot of your personal data from websites that you have set up accounts on can be scooped up in all the hacks or data breaches that are happening more frequently.
If you want to know what you could do to be online being tracked, I will provide you with some tools to stay online without being tracked. To be anonymous online is…to not go online at all. You want to be online, and you want to be anonymous to minimize spying, targeted ads, and ID theft.
Social Network Security
Facebook makes money by having many users looking at many ads and, from time to time, making your data available to other businesses. There are several steps you can take to regain some Facebook anonymity. In a browser, go to the Account menu in the upper right and select Settings > Privacy. Click the “Edit” link on every choice on this page to personalize who can see what, who can friend you, and even who can look you up. In your activity log, you can delete a post that you have made in the past. I have a habit of deleting old posts or likes I made. I just keep one year of data.
Facebook Checkup, click > Privacy Checkup. Under Timeline and Tagging, ensure that you don’t get tagged in images or posts without your permission.
Go to your General Account Settings, and click “Edit” next to every entry. Double-check the email address and phone numbers you have entered and minimize the list of who has access to maximize anonymity.
If you don’t want to use Facebook anymore, you can, delete the account. Deactivating it leaves your data on the site for your potential return. Go to this Facebook page and follow the instructions.
On LinkedIn, go to the Settings icon of your face in the upper right and select Settings & Privacy. In the center, select the Privacy tab.
On Twitter, don’t list your website or real email in your profile under Twitter Settings > Privacy and Safety to protect your tweets, meaning only those followers you approve get access to them. Protected tweets aren’t searchable, aren’t retweetable, and you can’t share permanent links to them with non-approved followers.
Using your mobile
To be safe, you should log out from all your accounts for apps on your mobile phone, especially Google, Apple or your social networks. They are tracking all your activities, If you want to be anonymous, dump your mobile
If you want to be anonymous on a mobile phone, choose a prepaid phone, also known as a burner. Even with a burner, calls are recorded, and you can be triangulated via GPS. The upside of a burner is not having your real name associated with the device, and you can change a burner as often as you can to be safe. Just dispose of the old burner when you get a new one.
Protect your network with a Firewall
You should always have a router on your home network, and a router uses Network Address Translation ( NAT) to assign an IP address to every device on your home network; those are visible only on that network. Most people have a router at home for sharing home Wi-Fi.
You could also use firewall software installed on your laptop, and you can also find firewalls as part of security suites. If you want absolute anonymity based on your OS, stop using Windows or macOS on the desktop, and move to a Linux distro that specializes in all forms of keeping your secret.
What does your computer give away?
Your computer, mobile or tablet gives away your IP address that, makes your approximate physical location known and probably your time zone and what language you speak-all good info for advertisers. Your browser can also report on your operating system, browser type, and what versions of software you run for browser plug-ins. It even reports on the fonts you have installed. All of which can add up to giving your system a unique fingerprint.
You can check this information on what your browser gives away at MyBrowserInfo or BrowserLeaks.com and EFF’s Panopticlick tool to see how well your browser and VPN are protecting you. To get better privacy, you can install Privacy Badger browser extension that will monitor sites that monitor you.
Have you ever heard of browser fingerprinting?
Passwords
To protect yourself online, you need to make sure your password is different from one website to another website. This will guarantee you that if one site is breached that you don’t need to go to all the websites you have accounts on to change the passwords. It can be a headache for most people to keep track of different passwords, you can use a password manager. I use Dashlane there are many good password managers to choose from.
Make sure that your browser is not storing your passwords for sites you have accounts on, depending on the browser you use, you can, in the settings menu, turn off the ability for the browser to store the passwords you use to access websites and services.
Using your Browser
Browsers store things like images, surfing history, passwords, downloads and cookie files, which can remember helpful things like settings and passwords. You should delete the data from time to time, I suggest you set aside a time once a week to do that.
Major browsers also have anonymous surfing modes, Chrome calls Incognito (Ctrl+Shift+N to access), Firefox calls it Private Browsing (Ctrl+Shift+P) and Microsoft Edge and Internet Explorer call it In Private browsing (also Ctrl+Shift+P). Using it will prevent the browser from saving info on pages visited, whatever you search for-passwords, cookies, downloads, and cached content like images.
Javascript embedded in web pages is bad, they can include tracking code for various purposes, making it a habit to deactivate the use of Javascript in your browser. If you have a website that you visit often that has Javascript, you can turn off javascript for selected sites using extensions like NoScript.
If you’re looking for a browser with some extra security, consider getting Brave, a safe and secure browser that blocks unwanted content by default and keeps count and have a private window with Tor. Even with more secure browsers, you are not entirely anonymous, but they do prevent sites from writing info to your computer, including cookies, which other sites can later read to figure out your browsing habits.
Tor is a free network of tunnels for routing Web requests and page downloads – it’s not the same as a VPN but might be even more secure when it comes to your identity. It’s supposed to make it impossible for the site you access to figure out who you are. Tor is not entirely foolproof – the theory is you could still be tracked by someone skilled enough.
Always keep your browser up to date.
Proxies and VPNs and Tor, Oh, My
The way to ensure outsiders don’t gather information about you while you’re browsing the web is to appear to be someone else in a different location. This is a virtual private network (VPN) connection.
VPN services give you the advantage of securing the traffic between your computer and servers and masking your IP address and location. For example, by connecting through my work VPN, sites believe I’m at the office even though I work from home. VPNs also double as a way to access location-blocked content- if you are in a country that can’t get the BBC iPlayer or Netflix, for example, a VPN would work for you.
When choosing the best vpns for torrenting, ensure that the VPN does not slow internet speeds, is not based in a country with laws that allow the government to seize user records, can safely hide your IP address, and supports P2P activity.
I use NordVPN, there are many VPN service options out there.
What about Anonymous Email
The email simply wasn’t built with security in mind, there are secure email services which use encryption to scramble what you send and require the recipient to have a password that decrypts your message.
If you want an email service that will handle encrypted messages for your Gmail, Virtru is one of the better ones. There are also other tools to encrypt web-based email, FlowCrypt and Mailvelope are browser extensions that will secure Gmail, Outlook.com, and Yahoo Mail.
SPAM is a killer, how to protect
Never, EVER click on a link in a spam message or even open a spam email-the best way to avoid spam is to never let them get your address. It’s almost impossible, but there are methods to mitigate it.
Number one is to utilize an alias or dummy email, which can be used with any service that requires an email address. You might be able to set one up if you own your domain name. In G Suite, for example, you have your primary address, like [email protected], but there’s the option to use [email protected] as an alias for online sign-ups, messages which can be forwarded to the main address. When spam begins to collect, change or kill that second address, there can be up to 30 aliases per individual. Gmail is a little more straightforward: you append something to the user name to make an alias. Turn [email protected] into [email protected]. Once the alias accumulates spam, filter it right into the trash.
A disposable address is convenient if you only need an alias for a short time. Free services like Mailinator create an address you can check for a short time.
In the end
If you’re concerned about getting tracked while you browsing around on the internet, the best option you have is to sign out of all the services you are automatically signed in out. This is especially important if you walking around with your mobile in town or elsewhere. Otherwise, the ad servers and cookies and so forth that are run by these services that you are logged into or their affiliates will pretty much know where and when you go online at all times. Signing in and signing out can be painful, and very few people do that, and that is exactly what Google, Facebook, Microsoft, and Apple are counting on so they can collect your private data on your behaviour online.

Tech Disillusionment
For four decades, I have worked in the tech industry. I started in the 1980s when computing...
A Poem: The Consultant's Message
On a Friday, cold and gray,
The message came, sharp as steel,
Not from those we...
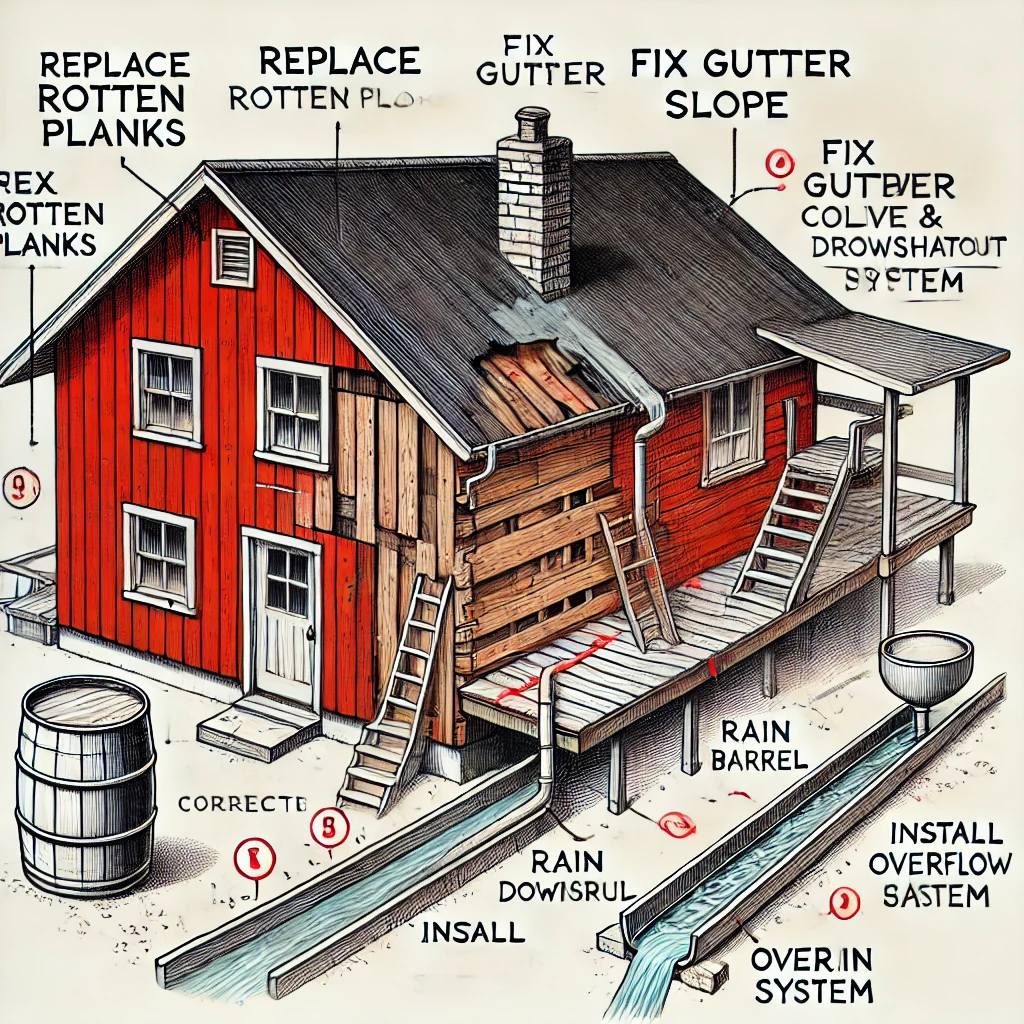
Using AI to Plan Wall Repair and Gutter Installation
In this article, I will share my experience using AI to plan the work required to fix a wall...